Helping IT Teams Procure Better Technology for Less
Your SMB or Enterprise IT, Simplified—From Procurement to Deployment, and Ongoing Support.

ITSelect is a trusted multi-brand provider of premier IT solutions and services, supporting SMB to Enterprise organizations across commercial and public sectors.



When technology falls short, better solutions are available.
If you have an IT product that's not performing, it may be time for an upgrade. Let’s fix that.
-
Request a new solution product quote. Better outcomes start with better technology.
-
Let's schedule a product demo with a vendor team to discuss your needs and learn more.
-
Ask about our L3 Remote and On-Site Support services, Retainer blocks are available.
-
When you are ready to get started — place an order.
Email product inquiries or pricing requests to info@it-select.com, or call us at 901-860-3636.

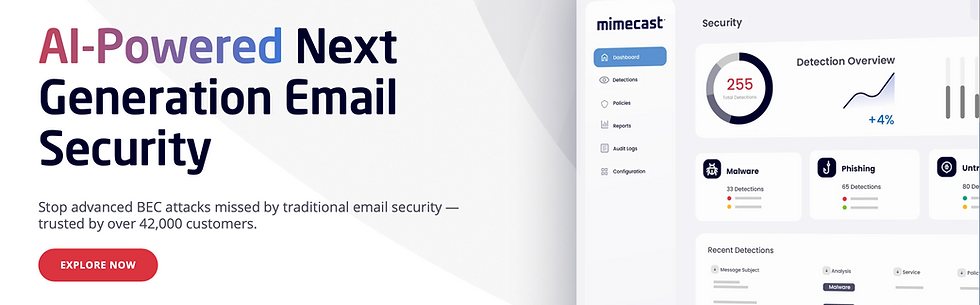
M365 Email Protection
Storage, Flash, NAS, and HCI
Network and Hardware Support
Networking and WLAN
Virtualization and Cloud
Data Protection and Backup